Posted in: Services > Other in Afghanistan | Posted: |
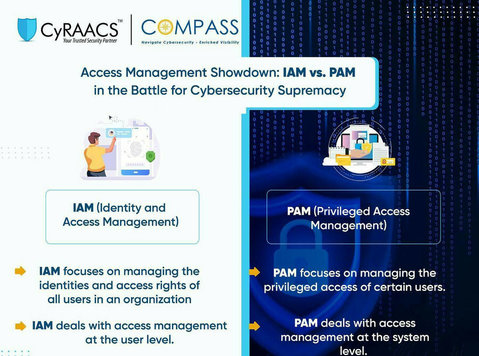
IAM: A set of security protocols and systems designed to manage digital identities and control access to IT resources. IAM ensures that only authorized users have access to sensitive data, systems, and applications.
PAM: A subset of IAM that specifically deals with managing access to high-level privileges, such as administrative accounts or system-level access. PAM focuses on securing the most sensitive access points within an organization’s IT infrastructure.
While IAM safeguards user identities, ensuring seamless access and protecting against unauthorized entry, PAM fortifies critical systems by managing and monitoring privileged access, thwarting potential cyber threats.
Which solution aligns with your organization’s security strategy? Join the conversation and share your insights!
Visit us for more details: https://cyraacs.com/
Contact this advertiser